What is CTB-Locker?
CBT Locker (or Curve-Tor-BitCoin Locker, or Critroni) is a ransomware that was released in June 2014 and has been operating till present. The ransomware targets Windows systems and is able to infect all versions of the OS released up to now.
What marks CBT-Locker out from other ransomware viruses is the encryption algorithm, which is ECC (Elliptic Curve Cryptography) instead of common RSA or AES codes. This encryption methods is more complicated and thus makes decryption next to impossible. The scanning for matching files is performed on all drive letters including removable storage devices. After the encryption CBT-Locker changes files extensions to .ctb or ctb2 for older versions of the virus or to a random extension in a current version.
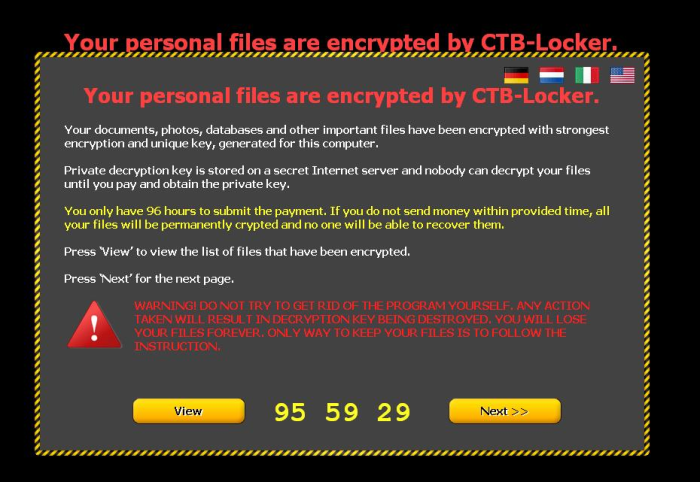
After the encryption comes the notification with a brief description of the situation and the instructions of payment. To make sure that user will get the message the ransomware adds a text file on desktop, in every folder, as well as it changes a victim’s wallpaper. Usually it states that a user has 96 hours to transfer 0.2 BitCoins, otherwise the ransomware will be eliminated together with the decryption code.
Still, we don’t recommend to rush to pay the ransom, as there are some tricks that you may perform first to remove CTB-Locker and restore your files.
CTB-Locker for Websites
In the beginning of 2016 a new version of CTB-Locker was released. This time cybecriminals chose websites as their aim. The ransomware first changes site’s original index.php and encrypts the information found on the site, including databases, scripts and documents. This time for the encryption key CTB-Locker demands 4 BitCoins. There is no expiration date for this ransomware, so it holds site as hostage until the ransom is paid. To avoid this you need to always have backups for your OS and all data.
How CTB-Locker got installed on your computer
According to the majority of reports, CTB-Locker is transported via infected emails. The subject and body of these messages may state that you have been sent a parcel, that you need to confirm a purchase or pay a tax. Recently these messages began to offer Windows 10 upgrade. The malicious file is attached to the email and contains a dangerous code. Once the attachment is opened, it installs the ransomware.
Symptoms of CTB-Locker infection
It’s difficult not to notice ransomware, since it often has one of the processes responsible for displaying a notification message. This window blocks the screen leaving the user minimum alternatives. Besides, some files will be inaccessible, as in many cases ransomware encrypts them to exasperate the scaring effect.
How to remove CTB-Locker?
To make sure that the adware won’t reappear, you need to delete CTB-Locker completely. For this you need to remove the files and registry entries of the ransomware. We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to CTB-Locker. It is not only the easiest way to eliminate CTB-Locker, but also the safest and the most assuring one.
Steps of CTB-Locker manual removal
Restart Windows in Safe Mode
For Windows 7, 8, XP and Vista:
- Restart the system
- While computer is rebooting press F8 several times
- In the appeared list of options choose Safe Mode
For Windows 10:
- In the Start menu click on the power button
- Hold Shift and choose Restart
- Choose Troubleshoot
- In the Advanced Options choose Startup Settings
- Click Restart
- Select Enter Safe Mode With Networking
Delete files and registry entries added by CTB-Locker
Now you will be able to reach the needed functions and files. For eliminating the ransomware activity, you need to find all of the following items and delete them.
Remove CTB-Locker files and folders:
%TEMP%\bqnvgig.exe
captec_invoice_2015_01_20-16_06.scr
brittlely.scr
%USERPROFILE%\Desktop\7ea9e7d0e7314c2ab5c23b100f60365d\wylam_invoice_2015_01_20-15_42.scr
%SystemDrive%\Users\jneuvel.CONFIA\AppData\Local\Temp\henrntk.exe
%TEMP%\jkylgdbirzboad.exe
%TEMP%\kb04009100.exe
%WINDIR%\ygehnnol.exe
%TEMP%\ljchyff.exe
%TEMP%\ochzigh.exe
%TEMP%\cjdolsd.exe
%TEMP%\eugqrwi.exe
%TEMP%\fzageih.exe
%TEMP%\kzjyswn.exe
%TEMP%\xlejyim.exe
%MyDocuments%\DecryptAllFiles [USER ID].txt
%MyDocuments%\AllFilesAreLocked [USER ID].bmp
%MyDocuments%\[RANDOM].html
%WinDir%\Tasks\[RANDOM].job
%Temp%\[RANDOM].exe
Users\[USER]\AppData\Local\[RANDOM].exe
Documents and Settings\[USER]\Application Data\[RANDOM].exe
Documents and Settings\[USER]\Local Application Data\[RANDOM].exe
Remove CTB-Locker registry entries:
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\System Security
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\System Components Update
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\mnvexhd
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{379B0208-4815-4A89-A2FE-2B8C6C6252D9}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Logon\{379B0208-4815-4A89-A2FE-2B8C6C6252D9}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{E076ED8D-7900-4AAA-B4A6-953642011552}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{A5538D18-5F5D-43EA-AFF1-A92F8D8DB134}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{1D1AC317-1966-4101-9F9E-7EBDC03AB61B}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{11C834B9-E673-4F9C-90BB-0E4FFA51F25E}
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Boot\{11C834B9-E673-4F9C-90BB-0E4FFA51F25E}
HKEY_CURRENT_USER\Control Panel\Desktop "Wallpaper" = "%MyDocuments%\AllFilesAreLocked [USER ID].bmp"
Restore the files encrypted by CTB-Locker
Use the decrypting tool
Unfortunately, currently the tool able to decrypt the files infected by CTB-Locker is not released yet. You may try applying to the methods described below, however, they might not work with the latest versions of CTB-Locker.
Restore the system
- Initiate the search for ‘system restore’
- Click on the result
- Choose the date before the infection appearance
- Follow the on-screen instructions
Roll the files back to the previous version
- Right-click the file and choose Properties
- Open the Previous Version tab
- Select the latest version and click Copy
- Click Restore