What is Yessearches.com?
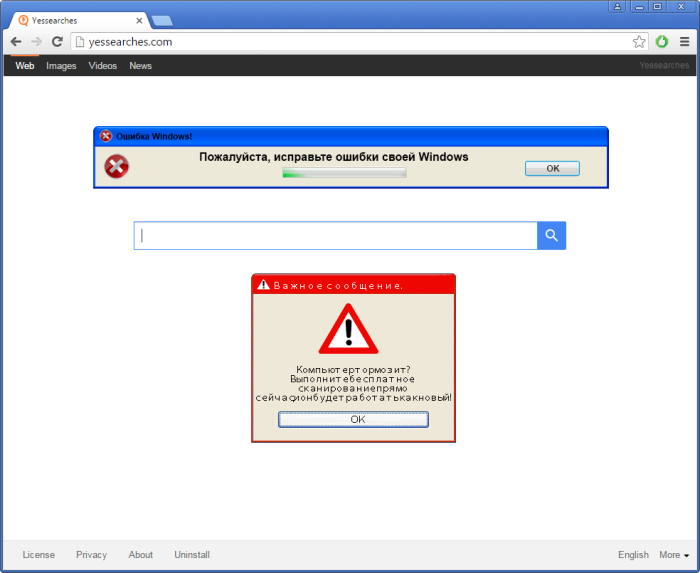
If you have recently noticed the change of the main page to yessearches.com and now are wondering whether you should use the new search engine or not, you should choose not to. The main reason for it is that the page belongs to the browser hijacker of the same name. Having it on your computer will cause redirections to the sites you probably would never visit willingly – the sources that are full of commercials and fake notifications. These sites may pretend to scan your system and find viruses that significantly damage your system, they would also offer to install rogue software in the likeness of antivirus programs. Or the hijacker may start to generate ads on the pages that were entirely safe before; anyway, it won’t let you to use the browser, whether it is Chrome, Firefox or IE, smoothly, that’s why you may want to remove Yessearches.com right after being infected.
How Yessearches.com got installed on your computer?
The point about all malware applications is that they almost can’t get to your system without you’re aiding it. The highest possibility of getting Yessearches.com is by installing some software that can be downloaded for free from the Internet. In fact you were even warned about it, but you didn’t pay attention. The End Users License Agreement always has the paragraphs explaining what consequences you will get installing the software. If you are not happy with any, you can go for Advanced installation mode to decline additional components.
Symptoms of Yessearches.com infection
- First and the most striking proof of having a browser hijacker is change of the main page. Usually it is a search engine page that is designed so that user would believe in its legitimacy.
- Generally, hijackers cause redirections when user makes a search query on its page or tries to reach a blocked site (usually another search engine or anti-malware sites)
- Another indicator of hijacker infection is appearance of new programs, toolbars and browser extensions that you don’t remember installing and processes in start-up queue.
- Also, you may notice the significant slowdown in the system operating, since running of the applications required for malware activity may consume a lot of CPU.
- Besides, hijacker infection may as well negatively affect the speed of Internet connection.
How to remove Yessearches.com?
To make sure that the hijacker won’t appear again, you need to delete Yessearches.com completely. For this you need to remove the application from the Control Panel and then check the drives for such leftovers as Yessearches.com files and registry entries.
We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to Yessearches.com. It is not only the easiest way to eliminate Yessearches.com, but also the safest and most assuring one.
Steps of Yessearches.com manual removal
Uninstall Yessearches.com from Control Panel
As it was stated before, more likely that the hijacker appeared on your system brought by other software. So, to get rid of Yessearches.com you need to call to memory what you have installed recently.
How to remove Yessearches.com from Windows XP
- Click the Start button and open Control Panel
- Go to Add or Remove Programs
- Find the application related to Yessearches.com and click Uninstall
How to remove Yessearches.com from Windows 7/Vista
- Click the Start button and open Control Panel
- Go to Uninstall Program
- Find the application related to Yessearches.com and click Uninstall
How to remove Yessearches.com from Windows 8/8.1
- Right-click the menu icon in left bottom corner
- Choose Control Panel
- Select the Uninstall Program line
- Uninstall the application related to Yessearches.com
How to remove Yessearches.com from Windows 10
- Press Win+X to open Windows Power menu
- Click Control Panel
- Choose Uninstall a Program
- Select the application related to Yessearches.com and remove it
 If you experience problems with removing Yessearches.com from Control Panel: there is no such title on the list, or you receive an error preventing you from deleting the application, see the article dedicated to this issue. Read what to do if program won’t uninstall from Control Panel
If you experience problems with removing Yessearches.com from Control Panel: there is no such title on the list, or you receive an error preventing you from deleting the application, see the article dedicated to this issue. Read what to do if program won’t uninstall from Control Panel
Remove Yessearches.com from browsers
Since some of hijacker threats use a disguise of a browser add-on, you will need to check the list of extensions/add-ons in your browser.
How to remove Yessearches.com from Google Chrome
- Start Google Chrome
- Click on Tools, then go to the Extensions
- Delete Yessearches.com or other extensions that look suspicious and you don’t remember installing them
How to remove Yessearches.com from Internet Explorer
- Launch Internet Explorer
- Click on the Tools/Gear icon, then select Manage Add-ons
- Delete Yessearches.com or other extensions that look suspicious and you don’t remember installing them
How to remove Yessearches.com from Mozilla Firefox
- Start Mozilla Firefox
- Click on the right-upper corner button
- Click Add-ons, then go to Extensions
- Delete Yessearches.com or other extensions that look suspicious and you don’t remember installing them
Reset your browsers
How to reset settings in Google Chrome
- Click on the icon in the right-upper corner
- Choose Settings
- Click Show advanced settings
- Click the Reset Settings button
How to reset settings in Mozilla Firefox
- Click the icon in the upper right corner
- Choose Help
- Select Troubleshooting Information
- Click the Reset Firefox… button
How to reset settings in Internet Explorer
- Click on the Tools button
- Go to Internet options
- Go to the Advanced tab
- Click Reset
Delete files and registry entries added by Yessearches.com
Sometimes removal via Control Panel is not enough since the built-in application can leave some files that shortly will restore the hijacker. So, you need to find all of the following items and delete them
Remove Yessearches.com files and folders:
\Program Files\searchestoyesbnd\@E9438230-A7DF-4D1F-8F2D-CA1D0F0F7924.xpi
\Program Files\searchestoyesbnd\bugreport.exe
\Program Files\searchestoyesbnd\ccuter.exe
\Program Files\searchestoyesbnd\ffuter.exe
\Program Files\searchestoyesbnd\shortboost.exe
\Program Files\searchestoyesbnd\unins.exe