How to remove Mumbefo.online
What Is Mumbefo.online?
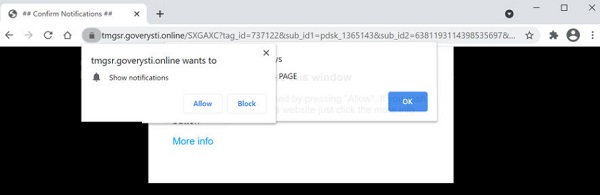
Mumbefo.online is a malicious website that tries to trick people into subscribing to messages displayed by the virus in order to send them with notifications to the desktop. Virus displays a pop-up window in the upper left corner to get permission to show notifications:
Mumbefo.online wants to Show notifications
Click Allow to confirm that you are not a robot!
If you allow displaying, your device activity will be significantly reduced due to the overload of unnecessary information. In addition, constant redirects and advertisements interfere with the normal operation of the Internet.
! You can remove Mumbefo.online automatically or manually. If you are an inexperienced user, then it is better to use the automatic method so as not to make a mistake!