How to remove Yourhotfeed.com
What is Yourhotfeed.com?
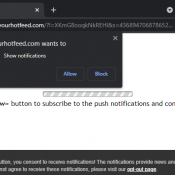
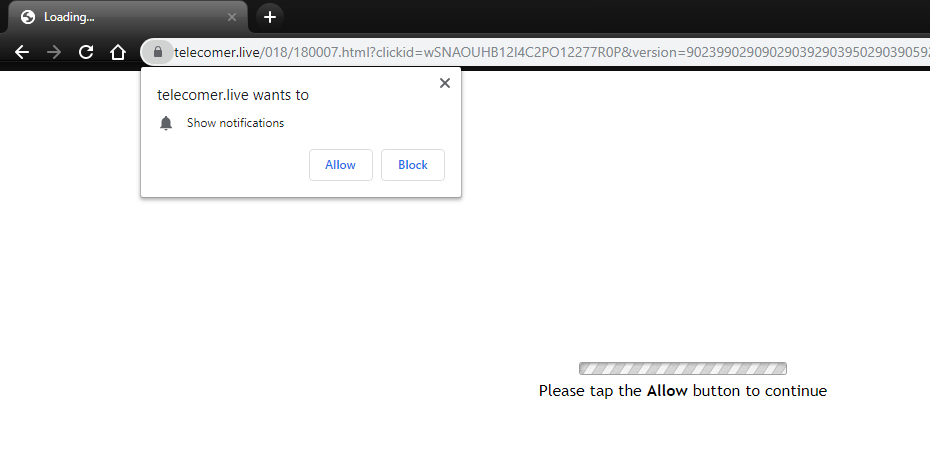
Yourhotfeed.com may start to appear in your browser from time to time and prompting to enable its notifications. This is supposedly necessary in order to open a page, to download a file, to play a video, etc. If you click the “Allow” button, Yourhotfeed.com notifications will start popping up in the lower right-hand corner of your screen occasionally, offering you to visit shady websites or download suspicious programs. These notifications will be delivered directly to your desktop whether your browser closed or not. If you are familiar with such problems, then your system is infected with adware. Adware often infiltrates users’ devices together with freeware programs users download from the Internet. You may follow this guide to uninstall adware and remove Yourhotfeed.com notifications from Google Chrome, Mozilla Firefox, IE, and Edge