How to remove ETH Ransomware and decrypt .ETH files

What is ETH Ransomware?
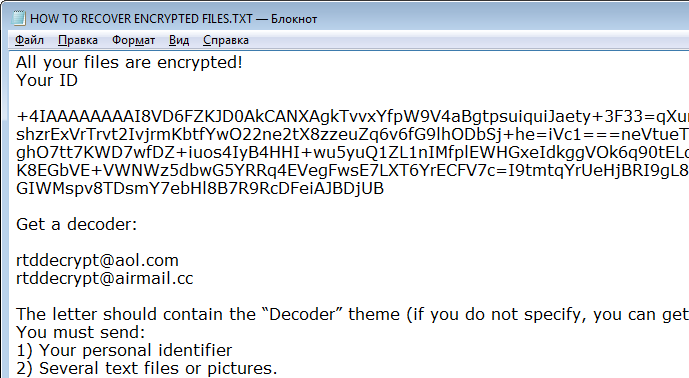
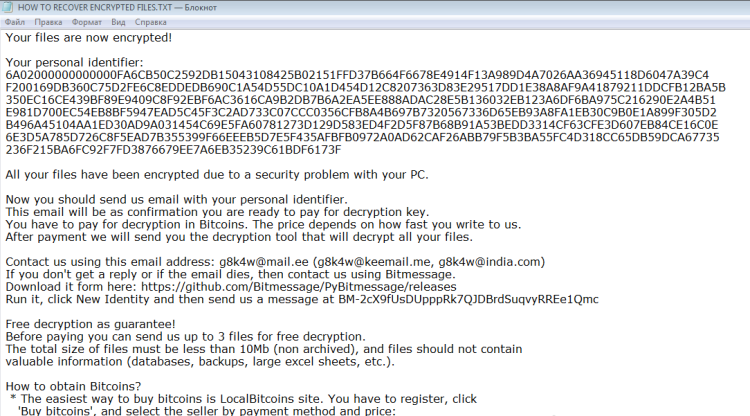
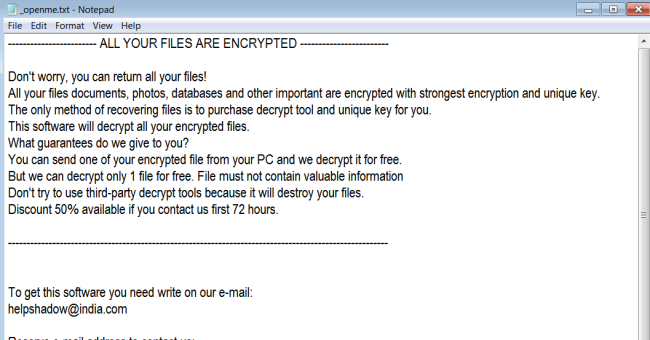
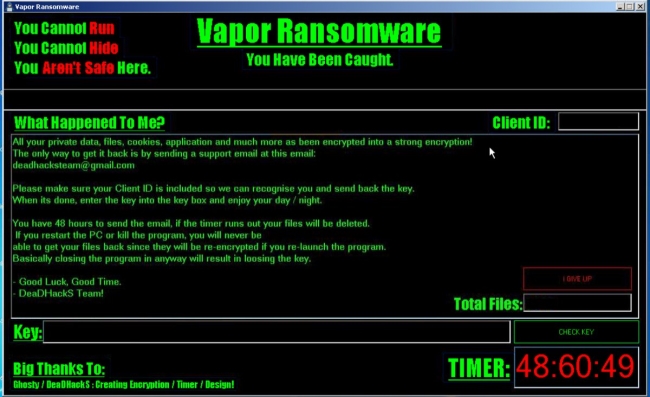
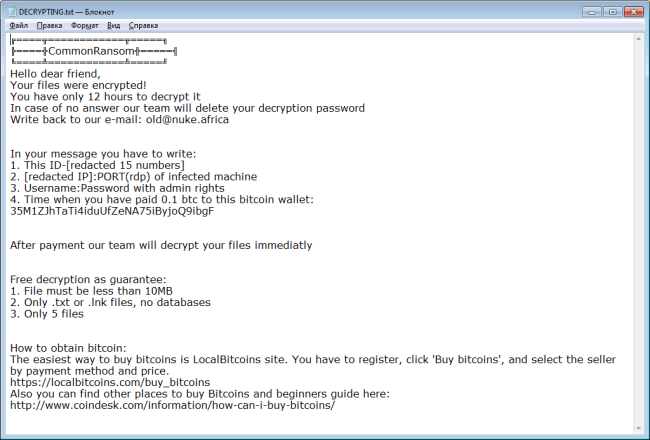
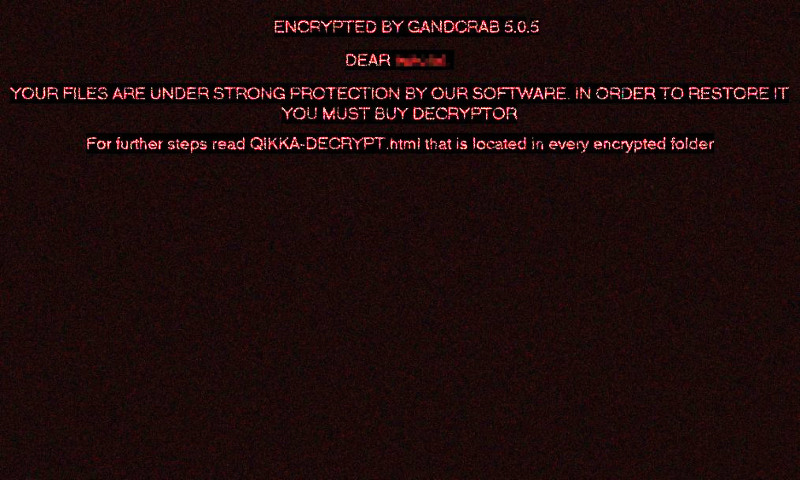
ETH Ransomware is a data-kidnapping malware that attacks users and encrypts their files. This type of virus is the most common at the moment as it allows to get high profit without being caught. The point is that all transactions proceed in bitcoins or other cryptocurrencies allowing cybercriminals to remain anonymous. ETH Ransomware often infiltrates users’ computers via infected emails and fake updates like Adobe flash update. Following infiltration, it will start infecting files using an encryption algorithm. As a result, all of the important files on a computer will become encrypted. If your computer is infected with this ransomware, let us warn you – do not spend any money on ransom, there are a lot of reports that cybercriminals just ignore their victims. Instead, you may try using this guide to remove ETH Ransomware and decrypt .ETH files without spending any money.