What is XiaoBa 2.0 Ransomware?
XiaoBa 2.0 is a new ransomware-virus that encrypts users’ data to make victims pay them. Today, the amount of ransom is 0.5 BTC (~$3969.99). To gain access to the user’s computer, cybercriminals use emails containing malicious files or links to the phishing sites. Following infiltration, XiaoBa 2.0 Ransomware immediately starts infecting targeted data, as a result of which, all your personal files become encrypted. The process ends with a note in 20 languages containing conditions for data releasing. In case if you have been attacked by XiaoBa 2.0 Ransomware, there is no need to contact cybercriminals and to make any concessions especially when you can decrypt your files for free. Remember, you are up against fraudsters who don’t care about your files and whose the main purpose is to make a profit. Hence, there is a high risk of being left without decryptor and money. Instead, you may try using this guide to remove XiaoBa 2.0 Ransomware and decrypt .XIAOBA files without spending any money.
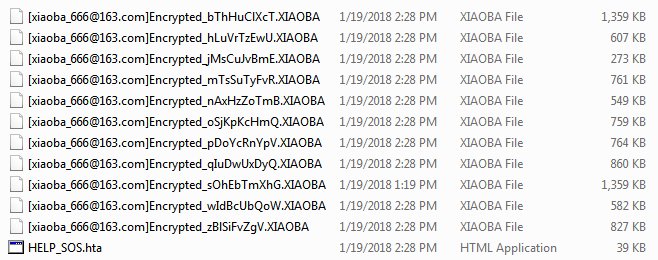
The principle of work of the ransomware is always the same – to encrypt files and then to require payment. XiaoBa 2.0 Ransomware encodes users’ personal files via RSA 4096 encryption algorithm. Each infected file gets extra extension according to the .[xiaoba_666@163.com]Encrypted_(random id).XIAOBA pattern. For example, file “myfamily.jpg” will turn into “myfamily.[xiaoba_666@163.com]Encrypted_(dfrtjhytj2d).XIAOBA”.
Example of encrypted files:
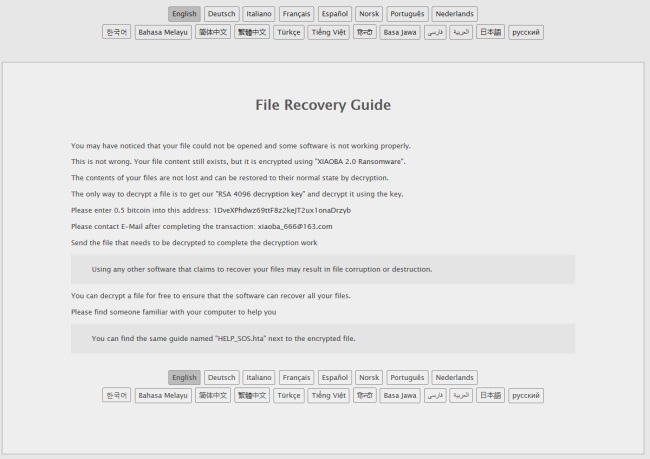
When it’s finished, ransomware creates HELP_SOS.hta, where the user may find the demands of criminals to decrypt encrypted files:
File Recovery Guide
You may have noticed that your file could not be opened and some software is not working properly.
This is not wrong. Your file content still exists, but it is encrypted using “XIAOBA 2.0 Ransomware”.
The contents of your files are not lost and can be restored to their normal state by decryption.
The only way to decrypt a file is to get our “RSA 4096 decryption key” and decrypt it using the key.
Please enter 0.5 bitcoin into this address: 1DveXPhdwz69ttF8z2keJT2ux1onaDrzyb
Please contact E-Mail after completing the transaction: xiaoba_666@163.com
Send the file that needs to be decrypted to complete the decryption work
Using any other software that claims to recover your files may result in file corruption or destruction.
You can decrypt a file for free to ensure that the software can recover all your files.
Please find someone familiar with your computer to help you
You can find the same guide named “HELP_SOS.hta” next to the encrypted file.
Although XiaoBa 2.0 is a really dangerous virus, you still have a good chance to get them back. Before deciphering, you should first stay focused on removing XiaoBa 2.0 Ransomware to avoid re-infection. Once XiaoBa 2.0 Ransomware is removed, you can proceed with decryption using one of methods provided below.
How to remove XiaoBa 2.0 ransomware?
To make sure that the ransomware won’t reappear, you need to delete XiaoBa 2.0 ransomware completely. For this, you need to remove the files and registry entries of the ransomware. We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to the automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to XiaoBa 2.0 ransomware. It is not only the easiest way to eliminate XiaoBa 2.0 ransomware but also the safest and the most assuring one.
How to decrypt .XIAOBA files
Restore files with Stellar Data Recovery
Data Recovery Pro is one of the most essential tools in the fight against ransomware-type viruses.
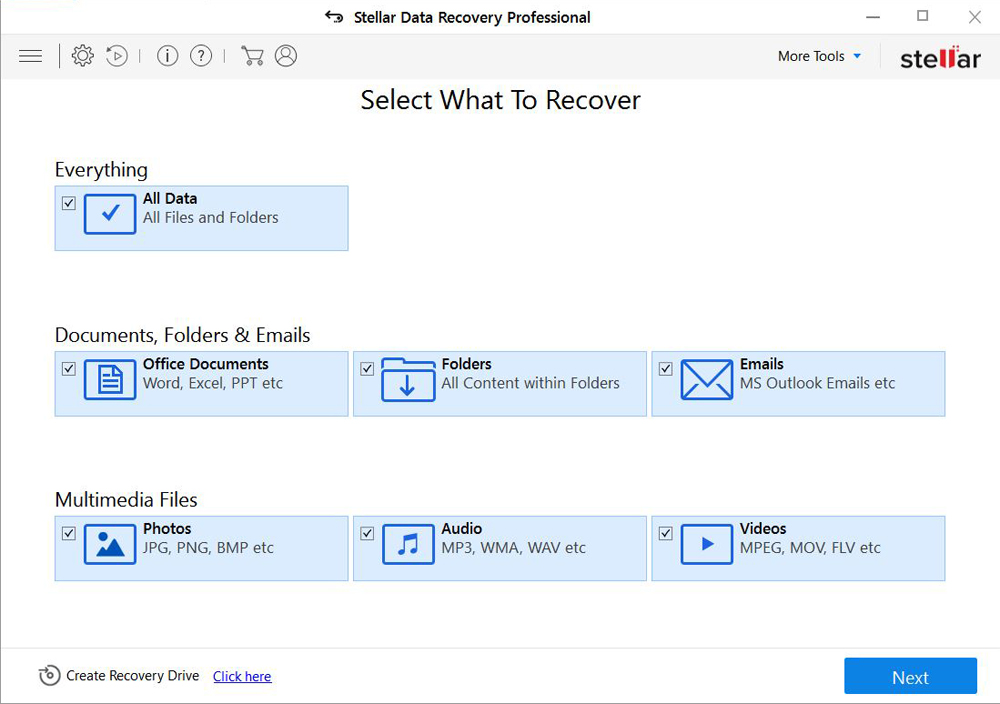
- Download Stellar Data Recovery and launch it
- Select the drive you want to recover and click START SCAN
- After scanning is finished, you are presented with a list of recoverable files found.
- Select the required files and click the Recover
Decrypt files using our decryption service
You may try using our own service for decrypting files compromised by ransomware-type viruses. The analysis of data takes 3-5 days, after which, we will let you know whether it’s decryptable or not. Note: the service is paid, payment is charged only for decryption, the analysis is free. In order to use our service, you should fill out the form listed below.
Also, please add a log file, created on your PC:
- Click “Start” and type: “cmd.exe” in the search box
- Right-click “cmd.exe” and select “Run as administrator“
- In command line, type or copy/paste following: dir C:\ /a/s > “%userprofile%\dirc.log”
- Find and attach the created “%userprofile%\dirc.log” file to the web form
Please attach encrypted text files according to the following conditions:
- number of files should not exceed 4;
- file size is not more than 8 megabytes;
- files must be from different folders;
- files must be unique.
Restore the system
- Initiate the search for system restore
- Click on the result
- Choose the date before the infection appearance
- Follow the on-screen instructions
Roll the files back to the previous version
- Right-click the file and choose Properties
- Open the Previous Version tab
- Select the latest version and click Copy
- Click Restore
If the above-mentioned methods didn’t help in eliminating the threat, then it’s better to rely on an automatic way of deleting XiaoBa 2.0 Ransomware.
How to prevent ransomware infection
To prevent infection with ransomware-type viruses, you should have proper antimalware software. This method is convenient because it allows you to detect a virus before it penetrates, and therefore to avoid infection and the loss of all your data. It is capable of protecting not only home computers but also server systems in large organizations. Download antimalware program to secure your system and privacy.