What is Turkish Ransomware?

Turkish Ransomware is cryptoworm that extorts money from victims in exchange for the decryption key. It belongs to the Scarab family which is well-known with a bad side in the computer world. According to the name, the new virus is focused on Turkish-speaking users, although they are unlikely to be able to read text in the ransom note. The thing is that ransom note was written in Notepad where there are no Turkish letters, as a result, they’ve been replaced with English letters. The encryption process goes unnoticed and once it is finished, all user files become inaccessible. To get back your files, you are forced to pay a sum of money in bitcoins. Actually, if you have been attacked by Turkish Ransomware, there is no need to contact them and especially to make any concessions. Remember, you are up against fraudsters who don’t care about your files and whose the main purpose is to make a profit. Hence, there is a high risk of being left without decryptor and money. Instead, you may try using this guide to remove Turkish Ransomware and decrypt .[firmabilgileri@bk.ru] files without spending any money.
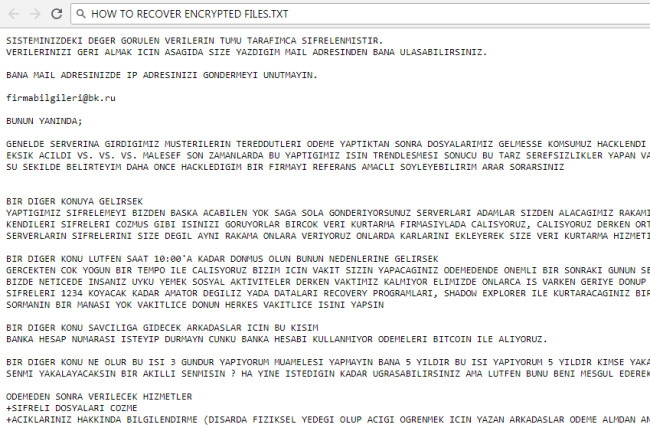
The principle of work of the ransomware is always the same – to encrypt files and then to require payment. Turkish Ransomware encodes users’ personal files via AES encryption algorithm. It is easy to recognize by “.[firmabilgileri@bk.ru]” extension which is added to each affected file. For example, file “myfamily.jpg” will turn into “myfamily.[firmabilgileri@bk.ru]”. After this, ransomware creates HOW TO RECOVER ENCRYPTED FILES.TXT file, where the user may find the demands of criminals to decrypt encrypted files:
SISTEMINIZDEKI DEGER GORULEN VERILERIN TUMU TARAFIMCA SIFRELENMISTIR.
VERILERINIZI GERI ALMAK ICIN ASAGIDA SIZE YAZDIGIM MAIL ADRESINDEN BANA ULASABILIRSINIZ.
BANA MAIL ADRESINIZDE IP ADRESINIZI GONDERMEYI UNUTMAYIN.
firmabilgileri@bk.ru
BUNUN YANINDA;
GENELDE SERVERINA GIRDIGIMIZ MUSTERILERIN TEREDDUTLERI ODEME YAPTIKTAN SONRA DOSYALARIMIZ GELMESSE KOMSUMUZ HACKLENDI DOSYALARI ACILMADI
EKSIK ACILDI VS. VS. VS. MALESEF SON ZAMANLARDA BU YAPTIGIMIZ ISIN TRENDLESMESI SONUCU BU TARZ SEREFSIZLIKLER YAPAN VAR PEKI BANA NASIL GUVENECEKSINIZ
SU SEKILDE BELIRTEYIM DAHA ONCE HACKLEDIGIM BIR FIRMAYI REFERANS AMACLI SOYLEYEBILIRIM ARAR SORARSINIZ
BIR DIGER KONUYA GELIRSEK
YAPTIGIMIZ SIFRELEMEYI BIZDEN BASKA ACABILEN YOK SAGA SOLA GONDERIYORSUNUZ SERVERLARI ADAMLAR SIZDEN ALACAGIMIZ RAKAMINDA USTUNE RAKAM EKLEYEREK
KENDILERI SIFRELERI COZMUS GIBI ISINIZI GORUYORLAR BIRCOK VERI KURTARMA FIRMASIYLADA CALISYORUZ, CALISYORUZ DERKEN ORTAKLIK VS. DEGIL SIZIN ONLARA GONDERDIGINIZ
SERVERLARIN SIFRELERINI SIZE DEGIL AYNI RAKAMA ONLARA VERIYORUZ ONLARDA KARLARINI EKLEYEREK SIZE VERI KURTARMA HIZMETINI VERMIS OLUYOR
BIR DIGER KONU LUTFEN SAAT 10:00'A KADAR DONMUS OLUN BUNUN NEDENLERINE GELIRSEK
GERCEKTEN COK YOGUN BIR TEMPO ILE CALISYORUZ BIZIM ICIN VAKIT SIZIN YAPACAGINIZ ODEMEDENDE ONEMLI BIR SONRAKI GUNUN SERVERLARININ HAZIRLANMASI SIFRELENMESI
BIZDE NETICEDE INSANIZ UYKU YEMEK SOSYAL AKTIVITELER DERKEN VAKTIMIZ KALMIYOR ELIMIZDE ONLARCA IS VARKEN GERIYE DONUP 1 ISLE UGRASAMIYORUZ SIFRELEDIGIMIZ VERILERIN
SIFRELERI 1234 KOYACAK KADAR AMATOR DEGILIZ YADA DATALARI RECOVERY PROGRAMLARI, SHADOW EXPLORER ILE KURTARACAGINIZ BIR SEKILDE BIRAKMIYORUZ YANI OYALANMANIN SAGA SOLA
SORMANIN BIR MANASI YOK VAKITLICE DONUN HERKES VAKITLICE ISINI YAPSIN
BIR DIGER KONU SAVCILIGA GIDECEK ARKADASLAR ICIN BU KISIM
BANKA HESAP NUMARASI ISTEYIP DURMAYN CUNKU BANKA HESABI KULLANMIYOR ODEMELERI BITCOIN ILE ALIYORUZ.
BIR DIGER KONU NE OLUR BU ISI 3 GUNDUR YAPIYORUM MUAMELESI YAPMAYIN BANA 5 YILDIR BU ISI YAPIYORUM 5 YILDIR KIMSE YAKALAYAMADI
SENMI YAKALAYACAKSIN BIR AKILLI SENMISIN ? HA YINE ISTEDIGIN KADAR UGRASABILIRSINIZ AMA LUTFEN BUNU BENI MESGUL EDEREK YAPMAYIN...
ODEMEDEN SONRA VERILECEK HIZMETLER
+SIFRELI DOSYALARI COZME
+ACIKLARINIZ HAKKINDA BILGILENDIRME (DISARDA FIZIKSEL YEDEGI OLUP ACIGI OGRENMEK ICIN YAZAN ARKADASLAR ODEME ALMDAN ANLATMIYORUZ)
DIPNOT: VAKIT VAKIT VAKIT EN ONEMLI SEY VAKIT SAAT 10 DEN ONCE DONUN.
Your personal identifier:
6A02000000000000***F5DED3F
firmabilgileri@bk.ru
Although Turkish is a really dangerous virus, you still have a good chance to get them back. Before deciphering, you should first stay focused on removing Turkish Ransomware to avoid re-infection. Once Turkish Ransomware is removed, you can proceed with decryption. Both automatic and manual solution is presented here that we hope will help you remove Turkish Ransomware and recover your files.
How Turkish ransomware gets on your PC?
This type of virus can be infiltrated through several methods, including a freeware software, spam messages, trojans, software from dangerous sources, etc. A process of installation can start hidden and automatically. Besides that, some malware programs can mark Turkish Ransomware as a trusted software program.
How to remove Turkish ransomware?
To make sure that the ransomware won’t reappear, you need to delete Turkish ransomware completely. For this, you need to remove the files and registry entries of the ransomware. We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to the automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to Turkish ransomware. It is not only the easiest way to eliminate Turkish ransomware but also the safest and the most assuring one.
How to decrypt .[firmabilgileri@bk.ru] files
Restore files with Stellar Data Recovery
Stellar Data Recovery is an essential tool in the fight against ransomware-type viruses that can recover encrypted files.
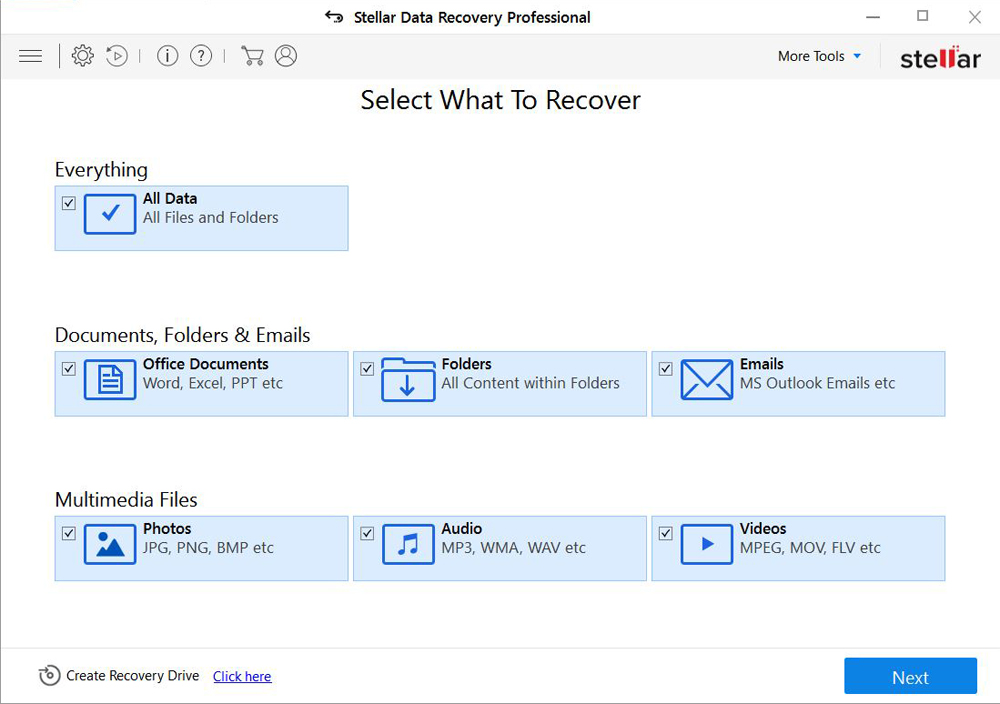
- Download Stellar Data Recovery and launch it
- Select the drive you want to recover and click START SCAN
- After scanning is finished, you are presented with a list of recoverable files found.
- Select the required files and click the Recover
Decrypt files using our decryption service
You may try using our own service for decrypting files compromised by ransomware-type viruses. The analysis of data takes 3-5 days, after which, we will let you know whether it’s decryptable or not. Note: the service is paid, payment is charged only for decryption, the analysis is free. In order to use our service, you should fill out the form listed below.
Also, please add a log file, created on your PC:
- Click “Start” and type: “cmd.exe” in the search box
- Right-click “cmd.exe” and select “Run as administrator“
- In command line, type or copy/paste following: dir C:\ /a/s > “%userprofile%\dirc.log”
- Find and attach the created “%userprofile%\dirc.log” file to the web form
Please attach encrypted text files according to the following conditions:
- number of files should not exceed 4;
- file size is not more than 8 megabytes;
- files must be from different folders;
- files must be unique.
Restore the system
- Initiate the search for system restore
- Click on the result
- Choose the date before the infection appearance
- Follow the on-screen instructions
Roll the files back to the previous version
- Right-click the file and choose Properties
- Open the Previous Version tab
- Select the latest version and click Copy
- Click Restore
If the above-mentioned methods didn’t help in eliminating the threat, then it’s better to rely on an automatic way of deleting Turkish Ransomware.
How to prevent ransomware infection
To prevent infection with ransomware-type viruses, you should have proper antimalware software. This method is convenient because it allows you to detect a virus before it penetrates, and therefore to avoid infection and the loss of all your data. It is capable of protecting not only home computers but also server systems in large organizations. Download antimalware program to secure your system and privacy.
[CBC show=”y” country=”ar,au,bb,bz,bo,ca,ky,cl,cn,co,cr,do,ec,gt,gy,ht,hn,hk,in,id,jm,jp,kr,my,mx,ms,ni,nz,pa,pe,ph,py,pr,sg,tw,th,tt,us,uy,ve,vn,vi”][/CBC]
[CBC show=”y” country=”fr”][/CBC]
[CBC show=”y” country=”de,at”][/CBC]
[CBC show=”y” country=”it”][/CBC]
[CBC show=”y” country=”nl,be”][/CBC]
[CBC show=”y” country=”es”][/CBC]
[CBC show=”n” country=”ar,au,bb,bz,bo,ca,ky,cl,cn,co,cr,do,ec,gt,gy,ht,hn,hk,in,id,jm,jp,kr,my,mx,ms,ni,nz,pa,pe,ph,py,pr,sg,tw,th,tt,us,uy,ve,vn,vi,fr,de,at,it,es,nl,be”][/CBC]