What is Aurora Ransomware?
Aurora is a name of the dangerous virus that, once installed, immediately encodes your files. After this, all your most important data such as documents, photos, videos become inaccessible. Thus, users fall victim to ransom demands ranging from $100 to $500. Still, you should never make concessions to these cybercriminals – there’s a strong possibility that you will end up with no money and cherished decrypter. Rather, you may follow these instructions that will help you to remove Aurora ransomware and decrypt .Aurora files without paying anything.
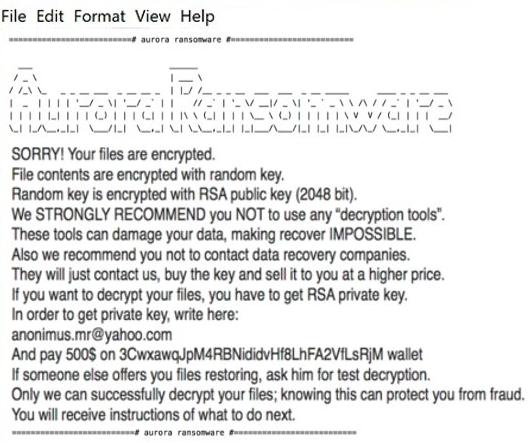
The principle of work of the ransomware is always the same – to encrypt files and then to require payment. Aurora Ransomware encodes users’ personal files via RSA-2048 encryption algorithm. It is easy to recognize by “.Aurora” extension which is added to each affected file. For example, file “myfamily.jpg” will turn into “myfamily.Aurora”. After this, ransomware creates multiple files on the desktop where the user will find instructions to decrypt encrypted files:
- HOW_TO_DECRYPT_YOUR_FILES.txt
- HOW_TO_DECRYPT_YOUR_FILES2.txt
- HOW_TO_DECRYPT_YOUR_FILES3.txt
- HOW_TO_DECRYPT_YOUR_FILES4.txt
- HOW_TO_DECRYPT_YOUR_FILES5.txt
- HOW_TO_DECRYPT_YOUR_FILES6.txt
- !-GET_MY_FILES-!.txt
===# aurora ransomware #===
Aurora Ransomware
—
SORRY! Your files are encrypted.
File contents are encrypted with random key.
Random key is encrypted with RSA public key (2048 bit).
We STRONGLY RECOMMEND you NOT to use any “decryption tools”.
These tools can damage your data, making recover IMPOSSIBLE.
Also we recommend you not to contact data recovery companies.
They will just contact us, buy the key and sell it to you at a higher price.
If you want to decrypt your files, you have to get RSA private key.
In order to get private key, write here:
anonimus.mr@yahoo.com
And pay 500$ on 3CwxawqJpM4RBNididvHf8LhFA2VfLsRjM wallet
If someone else offers you files restoring, ask him for test decryption.
Only we can successfully decrypt your files; knowing this can protect you from fraud.
You will receive instructions of what to do next.
===# aurora ransomware #===
Although Aurora is a really dangerous virus, you still have a good chance to get them back. Before deciphering, you should first stay focused on removing Aurora Ransomware to avoid re-infection. Once Aurora Ransomware is removed, you can proceed with decryption. Both automatic and manual solution is presented here that we hope will help you remove Aurora Ransomware and recover your files.
How Aurora ransomware gets on your PC?
This type of virus can be infiltrated through several methods, including a freeware software, spam messages, trojans, software from dangerous sources, etc. A process of installation can start hidden and automatically. Besides that, some malware programs can mark Aurora Ransomware as a trusted software program.
How to remove Aurora ransomware?
To make sure that the ransomware won’t reappear, you need to delete Aurora ransomware completely. For this, you need to remove the files and registry entries of the ransomware. We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to the automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to Aurora ransomware. It is not only the easiest way to eliminate Aurora ransomware but also the safest and the most assuring one.
How to decrypt .Aurora files
Restore files with Stellar Data Recovery
Stellar Data Recovery is an essential tool in the fight against ransomware-type viruses that can recover encrypted files.
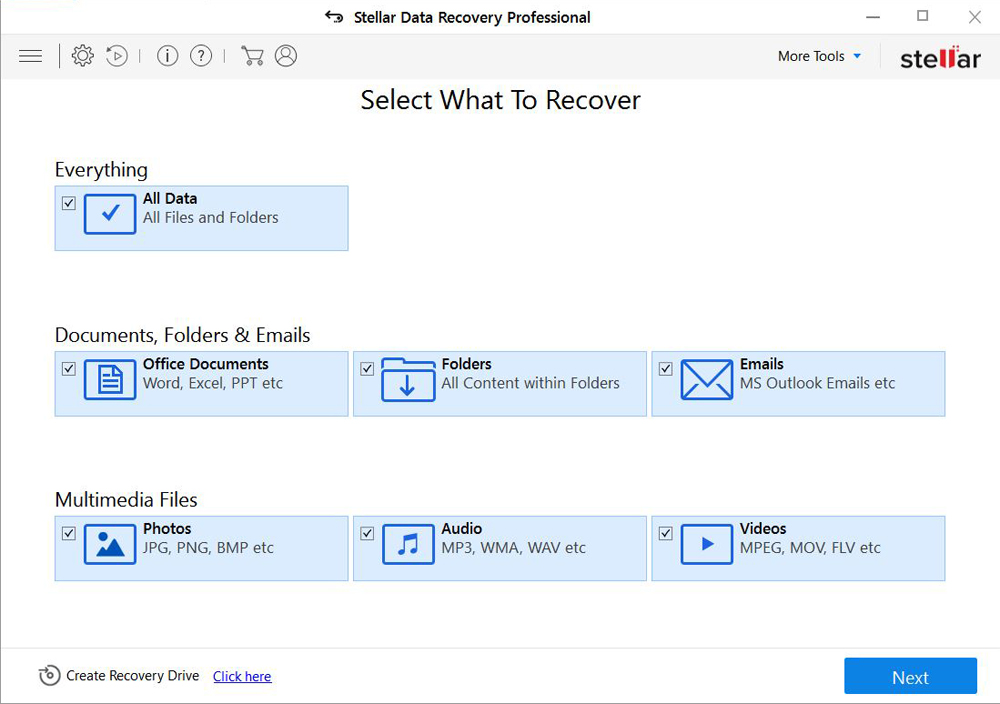
- Download Stellar Data Recovery and launch it
- Select the drive you want to recover and click START SCAN
- After scanning is finished, you are presented with a list of recoverable files found.
- Select the required files and click the Recover
Decrypt files using our decryption service
You may try using our own service for decrypting files compromised by ransomware-type viruses. The analysis of data takes 3-5 days, after which, we will let you know whether it’s decryptable or not. Note: the service is paid, payment is charged only for decryption, the analysis is free. In order to use our service, you should fill out the form listed below.
Also, please add a log file, created on your PC:
- Click “Start” and type: “cmd.exe” in the search box
- Right-click “cmd.exe” and select “Run as administrator“
- In command line, type or copy/paste following: dir C:\ /a/s > “%userprofile%\dirc.log”
- Find and attach the created “%userprofile%\dirc.log” file to the web form
Please attach encrypted text files according to the following conditions:
- number of files should not exceed 4;
- file size is not more than 8 megabytes;
- files must be from different folders;
- files must be unique.
Restore the system
- Initiate the search for system restore
- Click on the result
- Choose the date before the infection appearance
- Follow the on-screen instructions
Roll the files back to the previous version
- Right-click the file and choose Properties
- Open the Previous Version tab
- Select the latest version and click Copy
- Click Restore
If the above-mentioned methods didn’t help in eliminating the threat, then it’s better to rely on an automatic way of deleting Aurora Ransomware.
How to prevent ransomware infection
To prevent infection with ransomware-type viruses, you should have proper antimalware software. This method is convenient because it allows you to detect a virus before it penetrates, and therefore to avoid infection and the loss of all your data. It is capable of protecting not only home computers but also server systems in large organizations. Download antimalware program to secure your system and privacy.