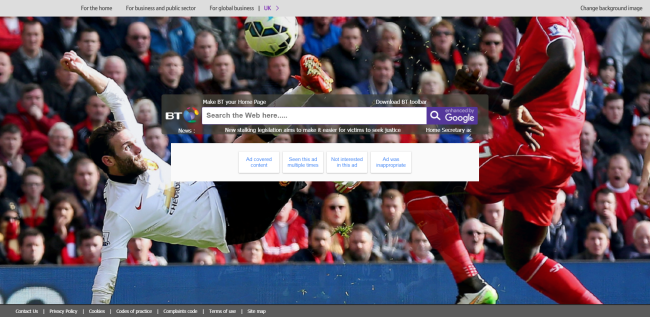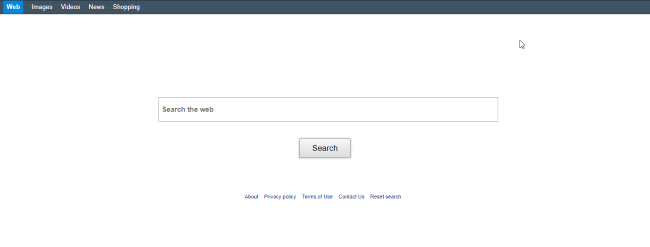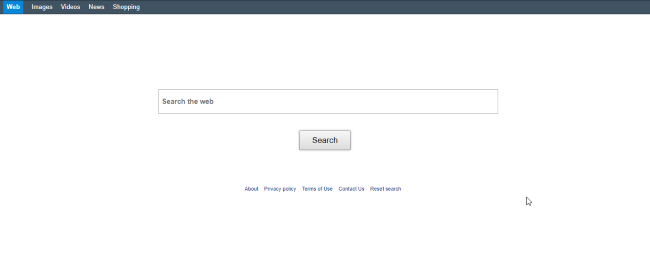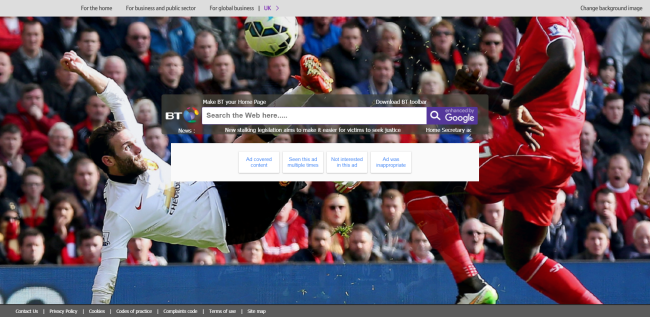
What is Search.bt.com?
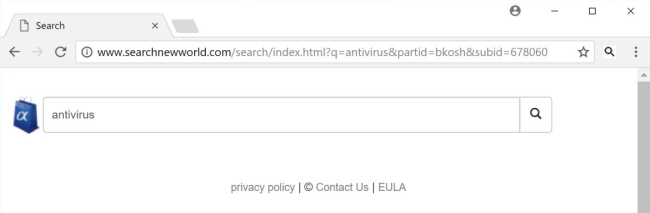
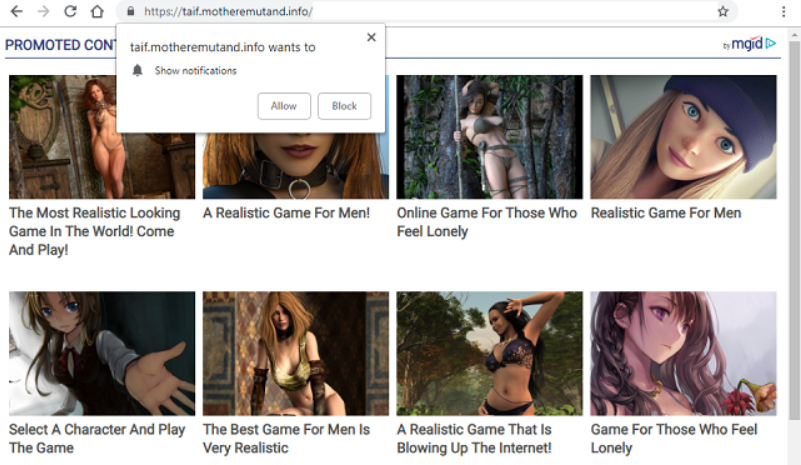
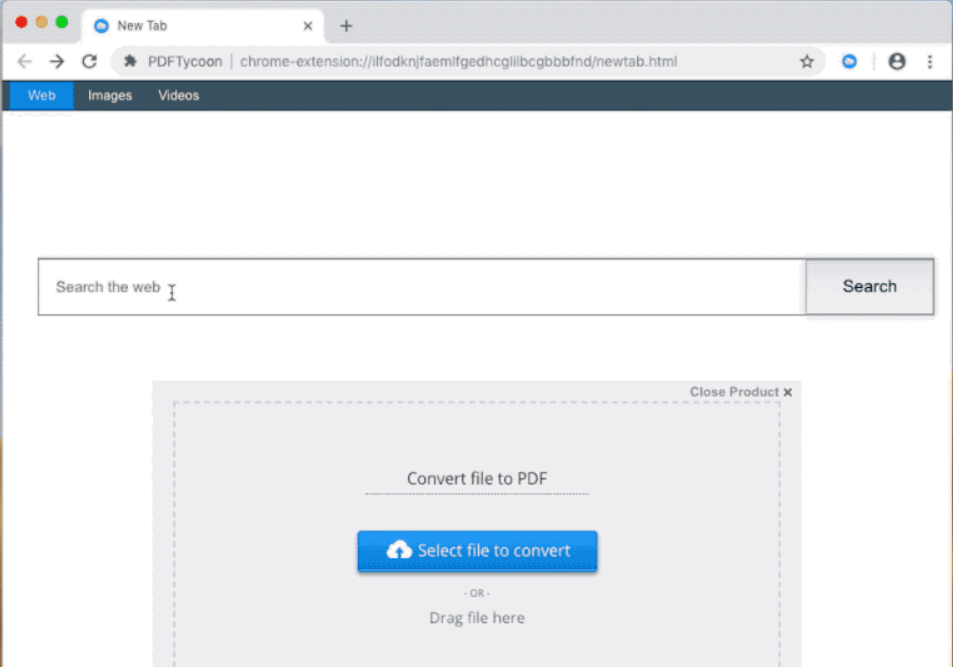
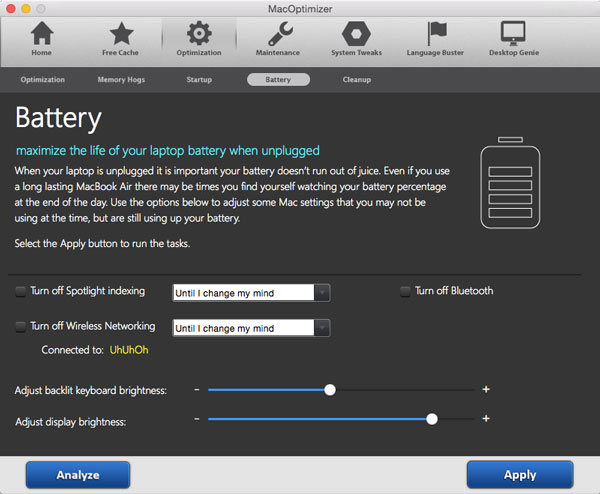
Today, there are many malicious applications called “browser hijacker” employ the same principle of masquerading their activities to a search engine. And we should agree that this technique works pretty fine – people who notice a new main page that looks like a trustworthy search domain, as a rule, do not rush to change it back and usually give a new source a chance. Despite the fact that Search.bt.com page design may have credibility on you, we warn you that it belongs to the hijacker of the same name. So, if you continue to use the page you soon will face the redirections to the sites that the malware promotes. Besides the fact that the sources to which the hijacker may redirect you would have nothing in common with your query, in addition, they may distribute other malware. In connection with this, we recommend to take immediate measures and remove Search.bt.com hijacker. read more