What is GandCrab Ransomware
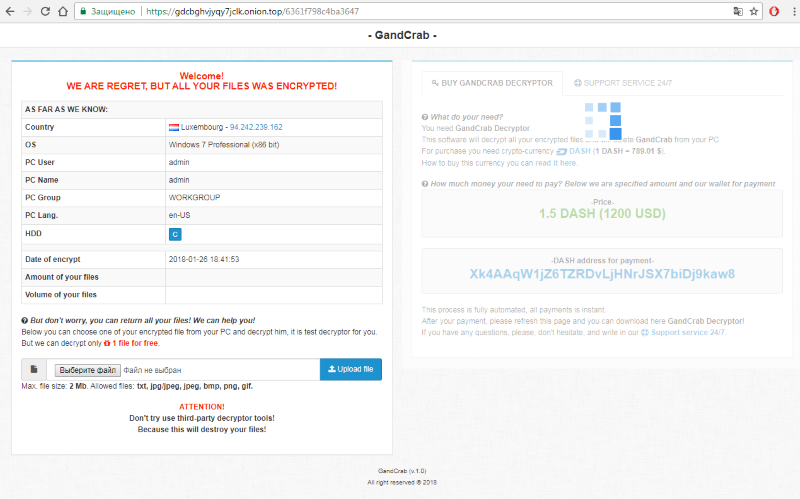
A GandCrab is a dangerous virus called ransomware. It encrypt users data on a thousand PCs and make impossible to read information in users files. Besides that, the virus creates and opens the text file, where shows operations to decode user’s files, usually by the bitcoin or Dash cryptocurrency payloads. A criminals says, that user has the only one way to get files back if he will pay. Users very rarely get decrypted data back, so we advice you not to pay them. Unfortunately, antiviruses often stay useless, and there are no universal tools capable of restoring all files, encrypted by a GandCrab Ransomware. Our advice is creating back up of all important files to prevent any loss by the virus. GandCrab is unique and has no similar ransomware, because it can delete restore points and users backup files. We recommend to remove GandCrab Ransomware and decrypt .GDCB files as soon as possible.
How GandCrab Ransomware gets on your PC?
This type of virus can be infiltrated through a macros in emails and office documents. Ransomware also going with malicious attachments, trojans, software from dangerous sources, etc. A process of installation automatically. Users don’t see these process, because virus hides it. Besides that, some unwanted programs from unknown sources can mark the GandCrab Ransomware as a trusted software program.
Symptoms of GandCrab Ransomware infection
It’s difficult not to notice ransomware since it often has one of the processes responsible for displaying a notification message. This window blocks the screen leaving the user minimum alternatives. Besides, some files will be inaccessible, as in many cases ransomware encrypts them to exasperate the scaring effect.
What to do if your PC is infected with GandCrab Ransomware
As soon as you notice the presence of the ransomware on your system, you should turn your computer off. If it is possible to try to create a backup or image of your hard drive info. This may let you to reserve the state of your drives in case a decryption method would be created afterward.
How to remove GandCrab Ransomware?
To make sure that the adware won’t reappear, you need to delete GandCrab Ransomware completely. For this you need to remove the files and registry entries of the ransomware. We should warn you that performing some of the steps may require above-average skills, so if you don’t feel experienced enough, you may apply to automatic removal tool.
Performing an antimalware scan with Norton would automatically search out and delete all elements related to GandCrab Ransomware. It is not only the easiest way to eliminate GandCrab Ransomware, but also the safest and the most assuring one.
Steps of GandCrab Ransomware manual removal
Restart Windows in Safe Mode
For Windows XP:
- Restart the system
- While computer is rebooting press F8 several times
- In the appeared list of options choose Safe Mode
For Windows 7 and Vista:
- Restart the system
- While computer is rebooting press F8 several times
- In the appeared list of options choose Safe Mode
For Windows 8 and 8.1:
- Restart the system
- While computer is rebooting press F8 several times
- In the appeared list of options choose Safe Mode
For Windows 10:
- In the Start menu click on the power button
- Hold Shift and choose Restart
- Choose Troubleshoot
- In the Advanced Options choose Startup Settings
- Click Restart
- Select Enter Safe Mode
How to decrypt and restore .GDCB files
Decrypt files using our decryption service
You may try using our own service for decrypting files compromised by ransomware-type viruses. The analysis of data takes 3-5 days, after which, we will let you know whether it’s decryptable or not. Note: the service is paid, payment is charged only for decryption, the analysis is free. In order to use our service, you should fill out the form listed below.
Also, please add a log file, created on your PC:
- Click “Start” and type: “cmd.exe” in the search box
- Right-click “cmd.exe” and select “Run as administrator“
- In command line, type or copy/paste following: dir C:\ /a/s > “%userprofile%\dirc.log”
- Find and attach the created “%userprofile%\dirc.log” file to the web form
Please attach encrypted text files according to the following conditions:
- number of files should not exceed 4;
- file size is not more than 8 megabytes;
- files must be from different folders;
- files must be unique.
Use the restoring tool
For those types of ransomware viruses that rather remove files than encrypt them we would suggest using Recuva program.
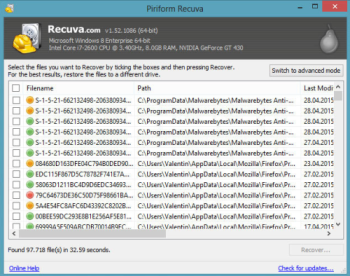
Recuva is a data recovery program for Windows, developed by Piriform. It is able to recover files that have been “permanently” deleted and marked by the operating system as free space.
- Download Recuva tool and launch it
- Within the on-screen wizard choose the type of the files you want to recover
- Choose the location of the files
- Wait until the application finishes scanning
- Select the required files and click the Recover button
Restore the system
- Initiate the search for system restore
- Click on the result
- Choose the date before the infection appearance
- Follow the on-screen instructions
Roll the files back to the previous version
- Right-click the file and choose Properties
- Open the Previous Version tab
- Select the latest version and click Copy
- Click Restore
If the above-mentioned methods didn’t help in eliminating the threat, then it’s better to rely on an automatic way of deleting GandCrab Ransomware.
We also recommend to download and use Norton to scan the system after GandCrab Ransomware removal to make sure that it is completely gone. The antimalware application will detect any vicious components left among system files and registry entries that can recover GandCrab Ransomware.