How to remove PooleZoor Ransomware and decrypt .poolezoor files

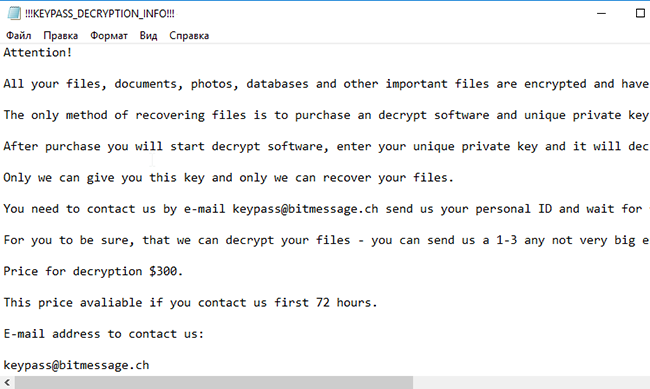
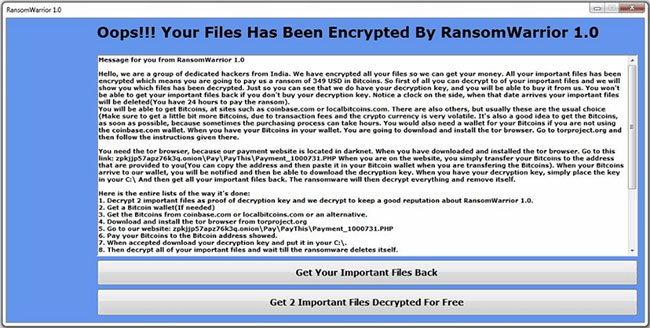
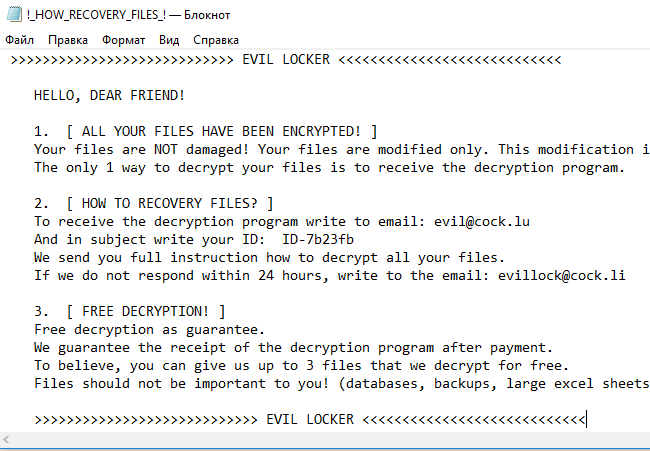
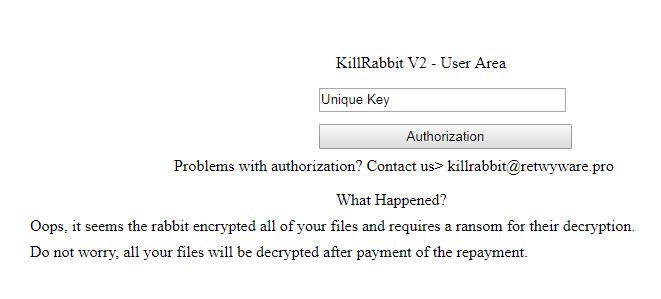
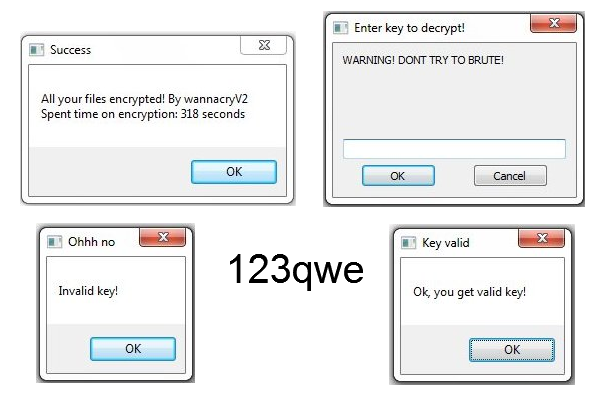
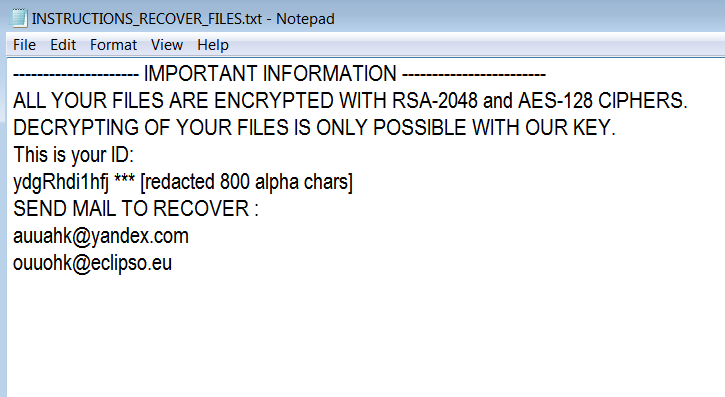
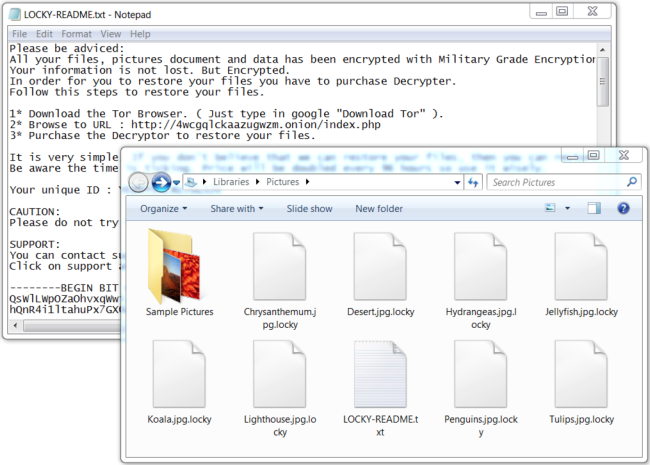
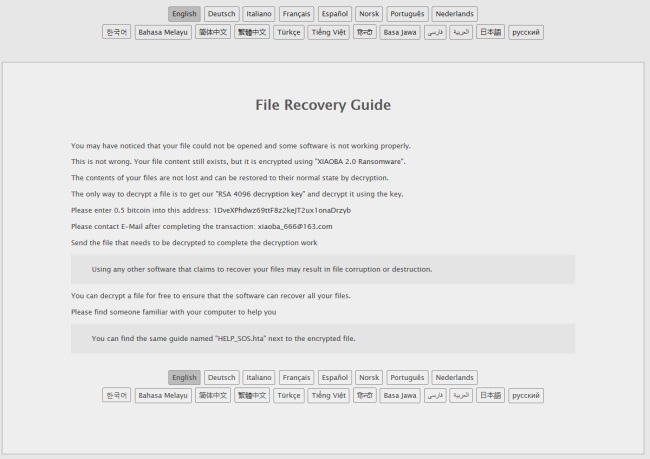
PooleZoor is a ransomware virus created by Iranian hackers that targets English-speaking users. This virus encrypts personal files on victim’s PC so that he can’t access them until all files are decrypted. To do this, users have to pay 10.000.000 Iranian rials that is approximately equal $237.50. However, we urgently advise you not to contact them and especially to make any concessions.